april 28, 2016
Changing Karotz Firmware (part one)
Note: messing around with firmware can damage your Karotz, or even brick it (so you cannot use it anymore). If you don't want to take this risk, it is safe to read these instructions, but do not try to execute the commands. I'm not responsible for any damage to your Karotz when you follow these instructions.
I'm lucky to have multiple USB-keys with firmware files. These keys were included with a few of the Karotz we bought last year, and were used by their owners for initial setup. The keys include the latest unmodified Violet/Mindscape firmware with version number 12.07.19.00.
The Karotz firmware consist of two main files:
- rootfs-12.07.19.00.tar.gz.gpg
- yaffs-12.07.19.00.tar.gz.
The first one "Rootfs" is the firmware that is flashed into the flash NAND memory of your Karotz.
The contents of the second file "YAFFS" are extracted to a writable part.
Both firmware files are compressed with gzip, and Rootfs is also signed with gpg. When we want to extract this file, we have to use a Karotz.
Normally, the autorun script of the USB-key will extract the files. So lets take a look at this file and find the lines to unsign and extract the Rootfs firmware file.
Look for lines 162-164, that's where the magic starts. We will copy these lines to a new (bash) script file and call the file "unsign.sh", and save it in /tmp of our Karotz. Line 164 needs a variable "$SERVER_ROOTFS_MAIN_BASENAME", so lets create and assign this variable in line 1 of our script. We also have to change the path to the firmware file: it is now pointing to the USB key, but we will copy the signed file to /tmp to extract it from there. So copy the file rootfs-12.07.19.00.tar.gz.gpg to /tmp on your Karotz (using WinSCP). Also transfer our unsign-script (unsign.sh) to /tmp with this content:
SERVER_ROOTFS_MAIN_BASENAME="rootfs-12.07.19.00.tar.gz"
SIGN=$(md5sum /karotz/etc/gpg/pubring.gpg | cut -d' ' -f1)
echo $SIGN | GNUPGHOME=/tmp/ gpg -d --logger-fd 2 --no-tty --passphrase-fd 0 /tmp/$SERVER_ROOTFS_MAIN_BASENAME.gpg > /tmp/$SERVER_ROOTFS_MAIN_BASENAME 2> /tmp/error.txt || ERROR "[USBKEY] bad $SERVER_ROOTFS_MAIN_BASENAME.gpg" ;
Use telnet to give it the right permissions (chmod 755) and run it. It will take a while, but when finished, we'll have a new file called "rootfs-12.07.19.00.tar.gz" which is now unsigned. Transfer this file from your Karotz to your PC. Open it (I use 7ZIP on Windows) and you'll find a tar file. Open the tar file, and you'll find two files:
- rootfs.img.gz
- zImage
zImage is written to /dev/mtd1 of your Karotz in autorun on line 177-180.
rootfs.img.gz is written to /dev/mtd2 of your Karotz in autorun on line 182-185.
We are interested in rootfs.img.gz, the Linux root filesystem of our Karotz.
The file rootfs.img.gz is a gzip compressed file. When extracted, we'll find rootfs.img. This file is a CRAMFS (Compressed ROM File System) file. When we want to make changes to it, we'll have to un-CRAM it and be able to re-CRAM it.
I first thought that this would be possible using a Windows tool. Unfortunately, I could not easily find such a tool for the Windows platform. Under Linux, this won't be a problem.
So we need a Linux machine. Lets create a virtual Linux machine. I installed Virtual Box as my virtualization platform. I created a new machine, and gave it 2048MB RAM memory. I then installed Ubuntu Desktop as an OS on my virtual machine.
Now we have a Linux machine, lets try to extract the CRAMFS image file.
We can extract CRAMFS files to a Linux filesystem using a utility called "cramfsck".
In your virtual Ubuntu machine, create a new directory called "Karotz-Firmware" and copy rootfs.img.gz into it. Use terminal and cd into the new directory (cd Karotz-Firmware). Enter the command "cramfsck".
You'll get a warning that this program is not installed. Install it with this command:
Now unzip the GZIP compressed image.
And extract the CRAMFS image:
This will extract the rootfs.img into a new directory called "firmware".
When you open the directory, you'll see Linux filesystem files and (sub)directories. But we cannot change anything, because we are not owner of these files. So lets make ourself owner of all the files:
Replace "username" with the name of the account you are currently logged in with (your Ubuntu user account name). And there it is, the Original Root Filesystem of the Karotz, ready to be changed to our needs.
You'll read more soon in part two. I'll explain how to change files, how to update Busybox and how to create a new image that can be flashed back to your Karotz. Stay tuned!
Images
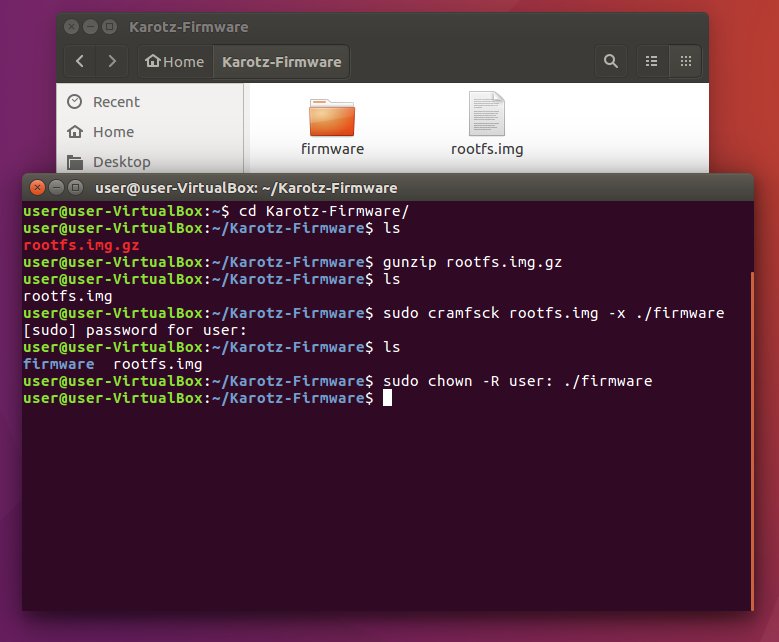
Extracting the Rootfs Firmware File.


